The topic I stopped running Tailscale in every container, and my home lab instantly became… is currently the subject of lively discussion — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
As my arsenal of free and open-source tools continues to expand with each passing week, I need a dedicated stack of services to monitor and manage the other utilities. Most of these admin apps tend to be locally-hosted as well, but there’s one tool that relies on external servers. And no, I’m not talking about my offsite TrueNAS, which runs on my own hardware.
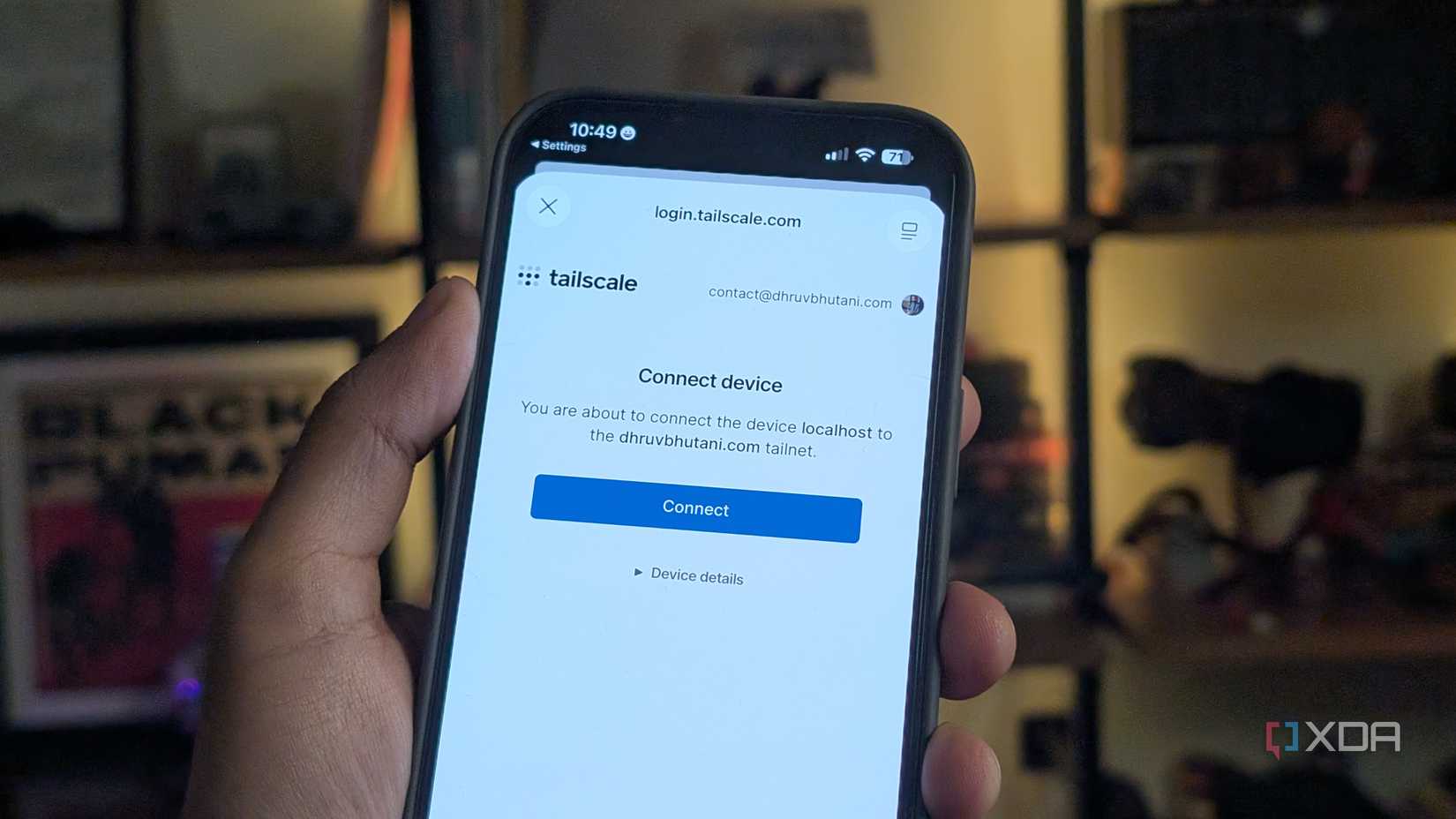
Rather, I’m talking about the Tailscale network that bridges all the nodes in my 3-2-1 backup pipeline and facilitates my remote access tasks while I’m away from my goblin cave. Although I’ve been using it for a long time, my initial Tailscale setup was drastically different from the one I currently have: I had the bad habit of arming my LXCs and VMs with Tailscale – one that I’ve gotten rid of after switching to a subnet router.
Back when I was a fledgling home labber, I’d tinker with as many cool repos I could find on GitHub, with VMs (and later on, LXCs) serving as the (unwilling) guinea pigs for my experiments. Considering that only a fraction of these applications were useful for my productivity needs, I never bothered to enable remote access for all my experiments. So, I’d simply install Tailscale on a handful of LXCs, while my laptop and NAS were the only bare-metal systems that needed this utility. On paper, keeping separate instances of Tailscale instead of a centralized subnet router seemed like a decent way to tinker with individual services.
However, both my home lab nodes and the virtual guests hosted on them have grown massively over the years – to the point where I’ve got entire clusters running everything from coding projects, unhinged experiments, and must-have productivity tools. Not to mention, I’ve also kept backup nodes at my family’s house, which run their own set of rsync tasks, PBS remote sync jobs, and monitoring tools. Installing Tailscale on every bare-metal rig alone would take a lot of time, and I’d probably lose what little remains of my sanity if I tried adding all the productivity and media-serving tools to my tailnet.
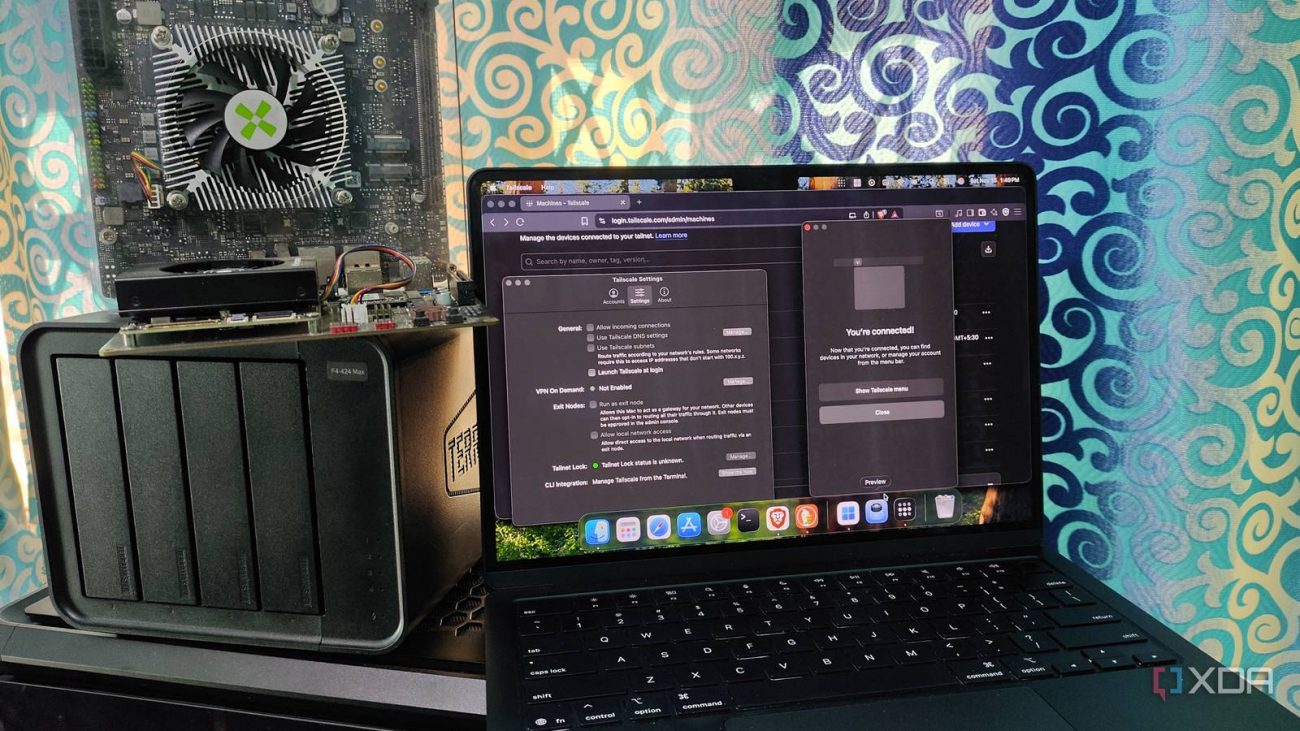
A few weeks ago, Tailscale updated its pricing system, with the free version receiving support for two additional users and ditching the max cap of 100 devices per tailnet. But I began thinning down my Tailscale nodes long before this change went into effect, and back then, I had dozens of systems hooked up to the same tailnet. Worse still, at least a quarter of them were inactive LXCs and cheap mini-PCs that I’d already armed with different server platforms. Granted, my allocated devices were below the maximum limit, but the fact that I had to scroll past several devices on the Tailscale admin panel just to work with the systems I actually use made me realize I’d over-complicated my tailnet – and it was high time I cleaned it up.
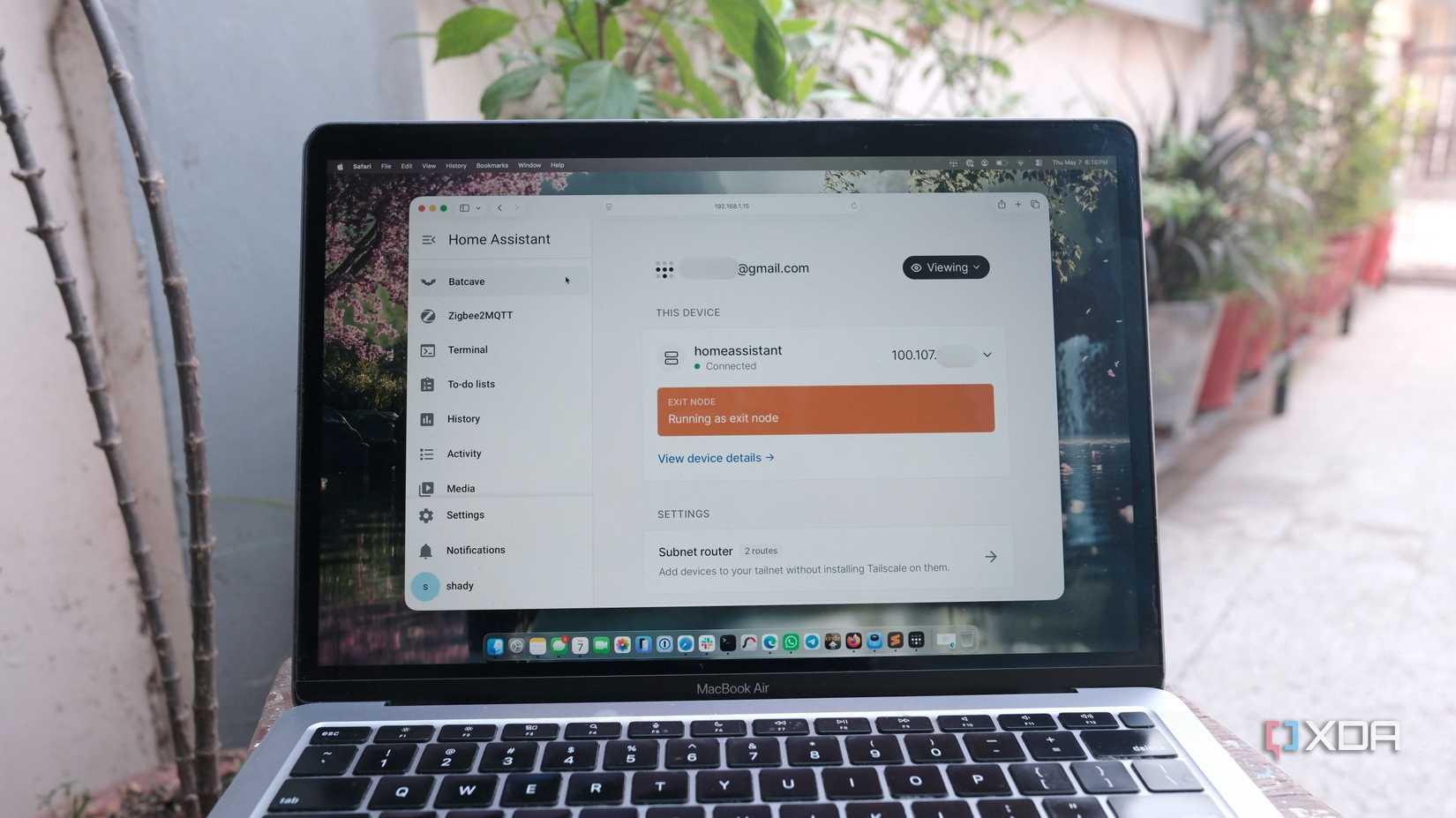
As its name implies, a subnet router allows every client in my tailnet to access the rest of the devices on the same subnet as the router – even if said systems don’t actually have Tailscale configured. Let’s say I configured an LXC as a subnet router. Any device connected to the same tailnet as this LXC would be able to access all the systems on my LAN. This spares me from enabling Tailscale on every device or navigating a maze of inactive devices on my admin panel. As long as I’ve got the right set of ACL (and firewall) rules, this subnet router becomes fairly safe from a security standpoint, too.
I host my subnet router on top of my OPNsense router, which includes a dedicated plugin for Tailscale. However, I’ve previously used an LXC-based subnet router, and it works just as well. That said, the setup process is a bit longer for unprivileged LXCs, as they require some extra permissions to use /dev/net/tun and other services for the subnet routing functionality.
Besides the subnet router functionality, the Tailscale ecosystem has a bunch of QoL services. I’ve set up my OPNsense router to double as an exit node, meaning it can route all the traffic from my client devices through my home network, thereby preventing curious tinkerers from snooping on my browsing activity while I’m frantically typing articles at a café. There’s also the Funnel facility, which lets me expose certain services to a public URL, with Tailscale handling the DNS and security certificates.