The topic Flatpak 1.16.4 patches a critical flaw that gave apps full host access is currently the subject of lively discussion — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
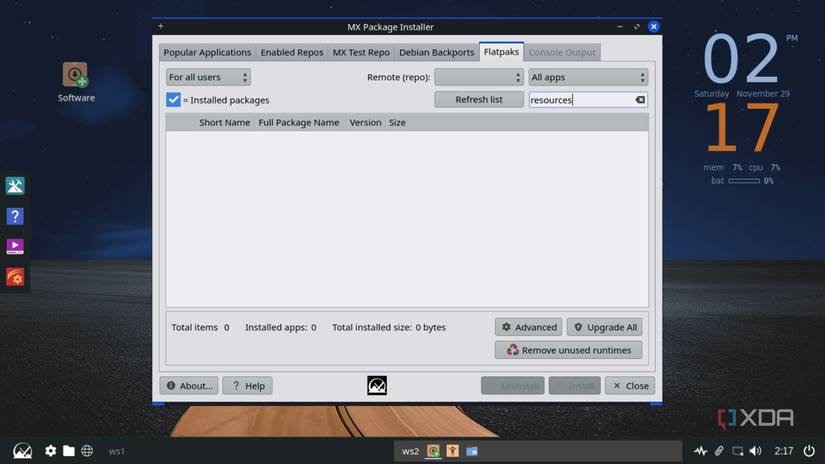
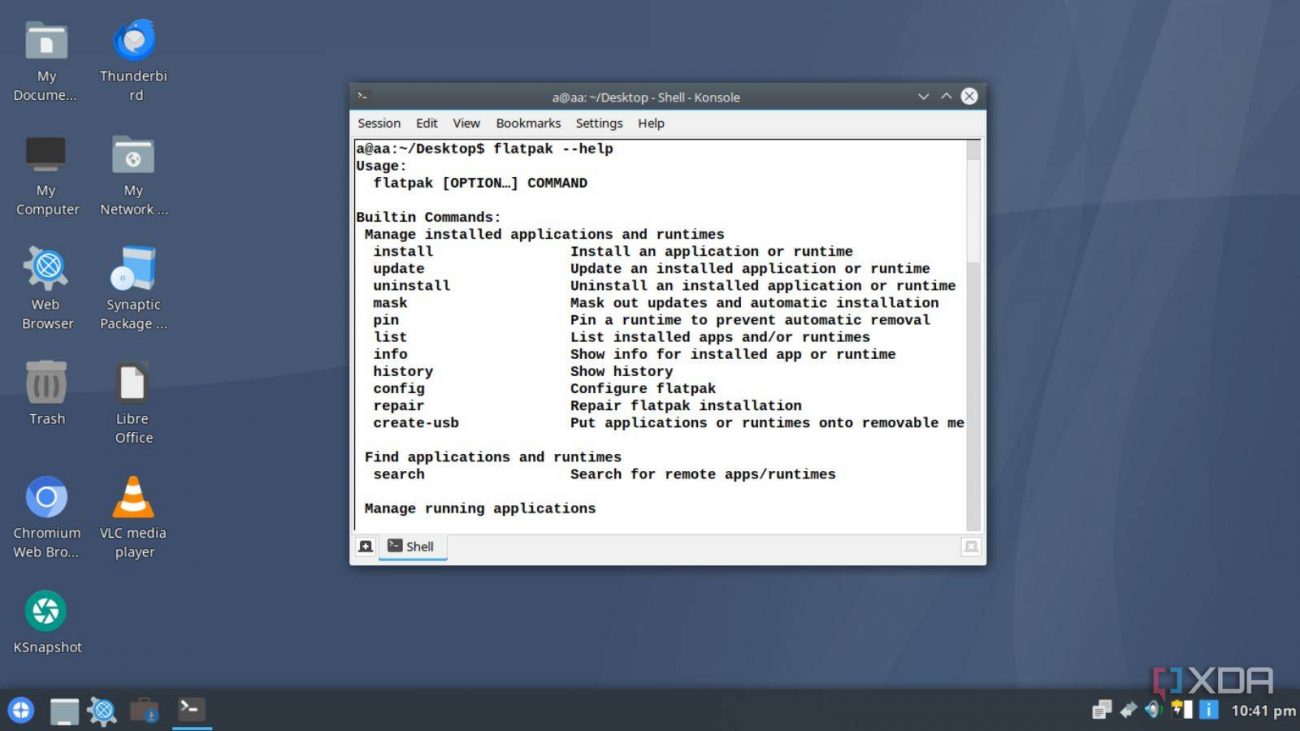
One of the biggest benefits of Flatpaks is how it puts apps into a container. It allows apps to ship with all of their dependencies and keeps them from altering your system files to install themselves, which are fantastic benefits; however, I’d argue the best reason to use Flatpaks is the privacy and security angle. You can control what a Flatpak can and cannot do through apps such as Flatseal, so your apps can’t access files or devices if you don’t want them to.
Unfortunately, Flatpak suffered a nasty exploit that would allow apps to get full host access and potentially run code on a PC. The good news is that the newest version of Flatpak, 1.16.4, introduces a fix for this bug, so be sure to give it a download if you’re concerned about your security.
As reported by Linuxiac, Flatpak version 1.16.4 has just been published on the project’s GitHub. It contains a few fixes, but the most important one stops an exploit that allows code to escape the confines of the Flatpak container. This allows an app to grant itself host file access and execute code as a host, which is exactly the kind of security issue people use Flatpak to avoid in the first place.
If you use Flatpak and you’d prefer not to download the update via GitHub, keep your operating system updated. The update should arrive through your regular channels soon enough.
It doesn’t have to be a winner-take-all debate. Using both changed how I manage Linux apps for the better.